Incident Response
When Something Goes Wrong, the Quality of Your Response Determines Whether It Becomes a Contained Event or a Catastrophic One.
A security incident is not a question of if — it is a question of when, what kind, and how prepared you are when it happens. The organizations that survive incidents with limited damage — contained breaches, minimal regulatory exposure, preserved client relationships, and manageable recovery costs — share one characteristic with each other that they don’t share with the organizations that don’t: they had a response capability in place before the incident occurred, not a plan they started building after the alerts fired.
The difference between a security incident and a material breach is almost always a function of detection speed and response quality, not the sophistication of the attack. The same ransomware variant, the same phishing campaign, the same credential compromise — deployed against two different organizations — produces dramatically different outcomes depending on how quickly the intrusion is detected, how effectively it is contained once detected, and how prepared the organization is to execute recovery while managing the regulatory, legal, and reputational dimensions of the event simultaneously. The organizations that experience incidents as learning events that strengthen their security posture are the ones that treated incident response as an operational capability to build and maintain, not an emergency procedure to improvise.
Lionhive’s Incident Response practice provides the preparation, detection integration, response execution, and post-incident analysis that determines which category your organization falls into when an incident occurs.
The worst time to figure out your incident response plan is during an incident. The worst time to discover your backup restoration hasn’t been tested is when you need it to work. The worst time to find out your cyber insurance policy requires a specific notification sequence is when you’ve already notified in the wrong order. Lionhive builds incident response capability before it’s needed — because the only time preparation is too late is after the incident starts.
The Regulatory Landscape for Incident Response
Incident response is no longer purely a technical function — it is a legal, regulatory, and operational function with mandatory timelines, specific notification requirements, and significant consequences for organizations that fail to meet them. Understanding the notification obligations that apply to your organization before an incident occurs is one of the most important aspects of incident response preparation.
SEC Cybersecurity Disclosure Rules — Public companies and registered investment advisors are required to report material cybersecurity incidents to the SEC within four business days of determining materiality on Form 8-K Item 1.05. Determining materiality — whether a reasonable investor would consider the incident significant to an investment decision — requires legal judgment under time pressure, which means the legal counsel, incident response team, and executive leadership need to be coordinating within hours of incident discovery, not days.
HIPAA Breach Notification Rule — Covered entities and business associates must notify affected individuals within 60 days of discovering a breach of unsecured protected health information, notify HHS on the same timeline for breaches affecting fewer than 500 individuals, and notify HHS within 60 days of year end. Breaches affecting 500 or more individuals in a single state require notification to prominent media outlets in addition to individual notification. The HIPAA definition of breach — and the four-factor risk assessment that determines whether an impermissible disclosure constitutes a reportable breach — requires careful analysis that must be completed within the notification window.
GDPR Article 33 — Organizations handling EU personal data must notify the relevant supervisory authority within 72 hours of becoming aware of a personal data breach — one of the most demanding notification timelines of any major privacy regulation. For US organizations with European customers, employees, or operations, GDPR notification obligations apply regardless of where the organization is headquartered.
Illinois PIPA and state breach notification laws — Every US state has a breach notification law with varying definitions of personal information, notification timelines, and content requirements. Illinois’s Personal Information Protection Act requires notification in the most expedient time possible and without unreasonable delay. Organizations operating across multiple states must satisfy the most demanding applicable requirements simultaneously.
FINRA and SEC financial services requirements — Broker-dealers and investment advisors face both the SEC material incident disclosure obligation and FINRA’s cybersecurity guidance requiring documented incident response procedures. The NY DFS 23 NYCRR 500 requires notification to the DFS Superintendent within 72 hours of a cybersecurity event that has a reasonable likelihood of materially affecting normal operations or that affects nonpublic information.
Lionhive’s incident response program is built around these notification obligations — ensuring that the timeline, sequencing, and documentation of every response action satisfies the applicable regulatory requirements for your organization’s industry and geographic footprint.
Lionhive’s Incident Response Capability
Incident Response Planning & Preparation
An incident response plan that exists as a document in a shared drive nobody has read is not an incident response capability. Lionhive builds incident response programs that are operational — written, tested, understood by the people who will execute them, and maintained as the organization and threat landscape evolve. The plan covers every phase of incident response for every material incident type — ransomware, credential compromise, data exfiltration, insider threat, business email compromise, third-party breach, and denial of service — with specific playbooks for each that define who does what, in what sequence, with what authority, and with what communication obligations.
Incident response preparation includes:
Incident Classification Framework — A structured approach to classifying incident severity that determines the appropriate escalation path, response resources, and notification obligations for each severity level. Consistent classification prevents both under-response to serious incidents and over-response to minor events — and produces the documentation that demonstrates measured, proportionate incident handling to regulators and insurers.
Roles and Responsibilities — Defined incident commander, technical response lead, legal counsel liaison, communications lead, and executive sponsor roles with clear authority and decision-making scope. Ambiguity about who is in charge of what during an active incident is one of the most common causes of poor response outcomes — it is resolved in the planning phase, not during the incident.
Communication Templates and Notification Sequences — Pre-drafted communication templates for internal notification, regulatory notification, client notification, and media response — reviewed by legal counsel before an incident occurs. The notification sequence is documented to satisfy the most demanding applicable regulatory timelines, so the team executing during an incident is following a pre-approved sequence rather than making ad hoc decisions about notification order under pressure.
Evidence Preservation Procedures — Documented procedures for preserving forensic evidence in a manner that maintains chain of custody for potential legal proceedings and regulatory investigations. Improper evidence handling during incident response can compromise the ability to understand what happened, identify the responsible parties, and demonstrate compliance with response obligations.
Cyber Insurance Integration — Coordination with your cyber insurance carrier’s incident response requirements — many policies require use of carrier-approved vendors, notification to the carrier within specific timeframes, and authorization before certain response actions. Failing to follow the carrier’s requirements can jeopardize coverage. Lionhive’s incident response planning integrates with your specific policy terms so the response team knows the carrier obligations before an incident triggers them.
Tabletop Exercises & Response Testing
An incident response plan that has never been tested is a hypothesis, not a capability. Lionhive conducts tabletop exercises that walk the incident response team — including executives, legal counsel, IT leadership, and communications — through realistic incident scenarios to test the plan, identify gaps, and build the muscle memory that determines how well people perform under the stress of an actual incident. Tabletop exercises surface the assumptions that turned out to be wrong, the communication bottlenecks that would slow response, the technical dependencies that weren’t documented, and the notification sequence questions that need legal resolution before they arise under four-hour deadline pressure.
For organizations subject to regulatory requirements that mandate incident response testing — including HIPAA, NY DFS, and NIST CSF 2.0 — tabletop exercise documentation provides evidence of active incident response program maintenance that satisfies examination requirements.
Active Incident Response
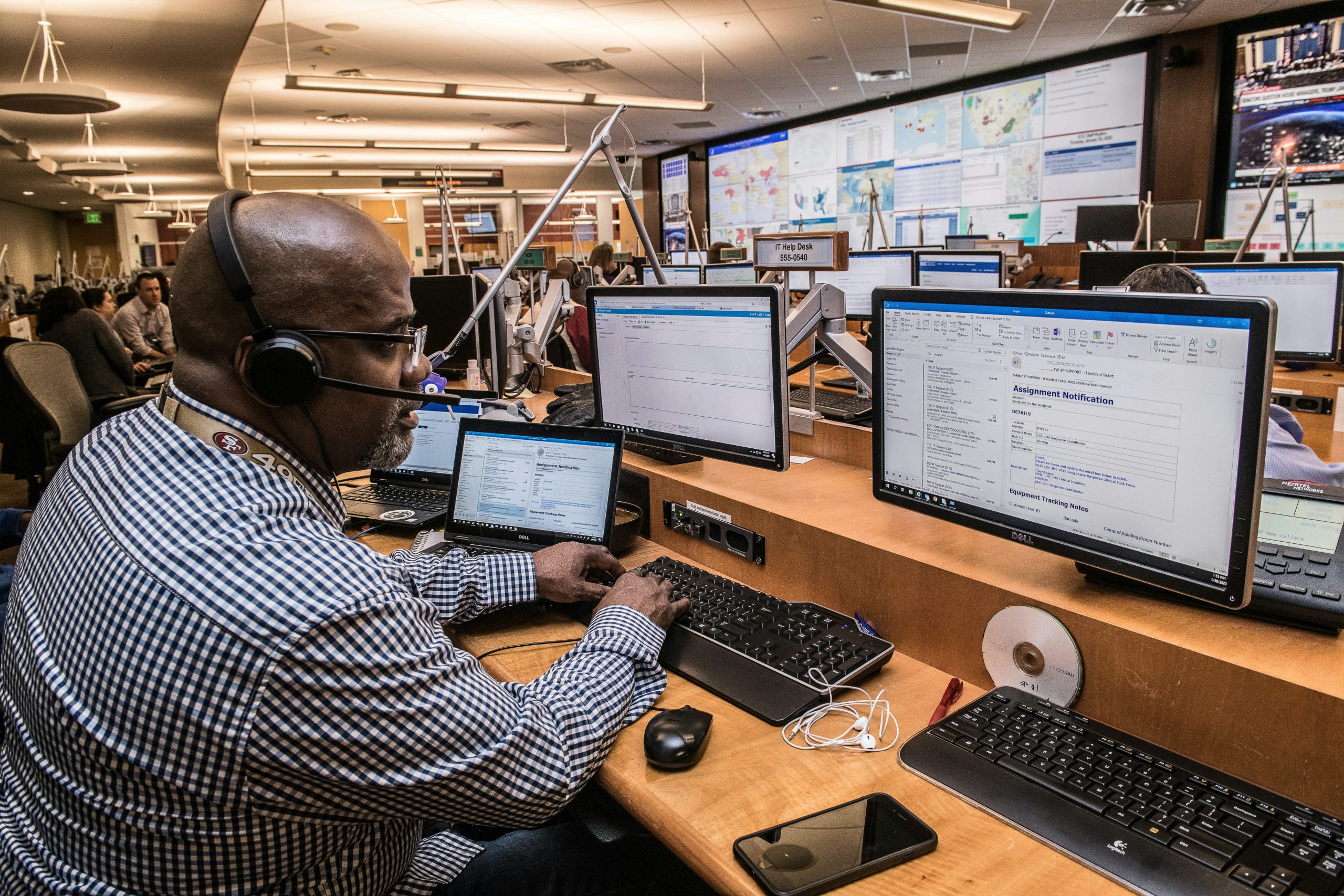
When an incident occurs, Lionhive provides the technical response capability to contain, investigate, and remediate — integrated with the Managed SOC detection infrastructure that identifies incidents as early as possible in the attack timeline. Active incident response covers:
Initial Triage and Scope Assessment — Rapid assessment of the nature, scope, and severity of the incident — what systems are affected, what data is at risk, what the attacker’s apparent objective is, and what the current state of the intrusion is. Accurate initial triage determines the appropriate response intensity and prevents both over-response that disrupts unaffected operations and under-response that allows an attacker to continue operating while the response team focuses on a limited subset of the compromise.
Containment — Isolation of affected systems, accounts, and network segments to stop the attacker’s ability to move laterally, exfiltrate data, or deploy additional payloads — while preserving the ability to investigate what has already occurred. Containment decisions involve real trade-offs between stopping attacker activity immediately and preserving the forensic evidence needed to understand what happened. Lionhive’s incident response team has the experience to make these trade-offs correctly under time pressure.
Forensic Investigation — Collection and analysis of forensic evidence to determine the full scope of the compromise — initial access vector, lateral movement paths, data accessed or exfiltrated, persistence mechanisms installed, and timeline of attacker activity. Forensic investigation answers the questions that regulators, legal counsel, cyber insurance carriers, and affected parties will ask — what happened, when did it happen, what data was affected, and how was it resolved. Without forensic investigation, organizations cannot answer these questions accurately and often over-notify or under-notify as a result.
Eradication — Removal of all attacker presence from the environment — malware, backdoors, persistence mechanisms, compromised credentials, unauthorized accounts, and configuration changes the attacker made during the intrusion. Incomplete eradication is one of the most common causes of re-compromise — organizations that restore systems without fully identifying and removing attacker persistence frequently experience a second incident within weeks of the first.
Recovery — Restoration of affected systems and services from clean backups or known-good states — with validation that restored systems are clean before returning them to production, and monitoring to detect any re-compromise during the recovery period. Recovery planning and backup architecture are addressed during incident response preparation — organizations that haven’t validated their backup restoration process before an incident discover during recovery that their backups weren’t working as expected.
Regulatory Notification Support — Coordination of the notification obligations triggered by the incident — drafting regulatory notifications, reviewing them with legal counsel, managing the notification timeline, and maintaining the documentation of notification actions that demonstrates compliance with applicable requirements. For incidents triggering SEC four-day disclosure, HIPAA 60-day notification, GDPR 72-hour notification, or NY DFS 72-hour notification, Lionhive’s incident response team manages the notification process in coordination with legal counsel to ensure timely, accurate, and legally defensible notifications.
Post-Incident Analysis & Program Improvement
Every incident contains information about the security gaps that made it possible and the response gaps that affected how it was handled. Lionhive conducts post-incident analysis after every significant incident — a structured review of what happened, what worked in the response, what didn’t, and what changes to the security program and response procedures would prevent recurrence or improve future response. The output is a prioritized remediation roadmap that addresses the specific gaps the incident exposed, not a generic security improvement checklist that ignores the specific context of what occurred.
Post-incident analysis documentation also serves the regulatory and legal purposes that arise after significant incidents — demonstrating to regulators, cyber insurance carriers, and potentially courts that the organization responded appropriately, learned from the incident, and took reasonable steps to prevent recurrence. For organizations subject to HHS OCR investigation following a reportable HIPAA breach, post-incident remediation documentation is a primary factor in OCR’s determination of corrective action requirements and penalty assessment.
Incident Response & Cyber Insurance
Cyber insurance is increasingly a primary driver of incident response investment — both because carriers require documented incident response capabilities as a condition of coverage, and because the quality of the response directly affects the size of the insurance claim. Organizations with mature incident response programs — faster detection, more effective containment, cleaner eradication, documented notification compliance — consistently experience lower breach costs and more favorable insurance outcomes than those without.
Lionhive’s incident response program is designed with cyber insurance requirements in mind — ensuring that response procedures, documentation practices, and notification sequences align with carrier requirements and produce the evidence portfolio that supports claim processing. For organizations navigating a cyber insurance claim following an incident, Lionhive provides the forensic documentation, response timeline, and remediation evidence that the claims process requires.
🌐 Why Organizations Choose Lionhive for Incident Response
- Integrated with Managed SOC — the team that detects incidents manages the response, eliminating handoff delays
- Regulatory notification expertise — SEC four-day, HIPAA 60-day, GDPR 72-hour, NY DFS 72-hour, and state breach notification laws
- Tabletop exercises that test plans before incidents make the gaps expensive
- Forensic investigation that answers the questions regulators, insurers, and counsel will ask
- Cyber insurance integration — response procedures aligned with carrier requirements before a claim is filed
- Post-incident analysis that produces a prioritized remediation roadmap, not a generic checklist
- HIPAA, SOC 2, NIST CSF 2.0, FINRA, SEC, NY DFS, and CMMC compliance documentation throughout
📞 Ready to Build a Response Capability Before You Need It?
The organizations that handle incidents well aren’t lucky — they’re prepared. If your incident response plan hasn’t been reviewed in the last 12 months, hasn’t been tested with a tabletop exercise, doesn’t have documented notification sequences for your specific regulatory obligations, or doesn’t exist yet — let’s talk about building the capability before it’s tested by an actual incident.
👉 Book an Incident Response Assessment
Part of Lionhive’s Cybersecurity & Compliance practice — see also Managed SOC, Zero Trust Architecture, Vulnerability Management, Dark Web Monitoring, and NIST CSF.
